a16z: 5 Principles of Cryptocurrency Custody 1. **Security**: Implement industry-leading security measures to protect assets from theft and unauthorized access. 2. **Compliance**: Adhere to all relevant regulations and compliance requirements to ensure
Original Article Title: Holding the future: Custody principles for a tokenized world
Original Article Authors: Scott Walker, Kate Dellolio, David Sverdlov
Translated by: Luffy, Foresight News
Registered Investment Advisors (RIAs) investing in crypto assets face a dilemma of unclear regulations and limited asset custody options. What's more complex is that crypto assets come with ownership and transfer risks different from the assets RIAs have traditionally been responsible for. RIAs' internal teams (operations, compliance, legal, etc.) are struggling to find willing and compliant third-party custodians to meet their expectations. Despite their efforts, they find it challenging to identify qualified custodians, leading RIAs to self-custody these assets. As a result, current crypto asset custody faces unique legal and operational risks.
What the crypto industry needs is a principled approach to help institutional investors safeguard crypto assets. In response to the recent Securities and Exchange Commission (SEC) request for information, we have developed some principles that, if implemented, would extend the objectives of the Investment Advisers Act custody rule to the new category of crypto assets.
How Crypto Asset Custody Differs
The control of traditional assets by their holders means that others do not have control. However, this is not the case with crypto assets, where multiple entities may have access to the private keys associated with a set of crypto assets.
Crypto assets also often come with various intrinsic economic and governance rights crucial to the assets. Traditional debt or securities can passively earn income (such as dividends or interest), and holders do not need to transfer the assets or take any further action after acquiring them. In contrast, crypto asset holders may need to take actions to unlock specific income or governance rights associated with the assets. Depending on the capabilities of the third-party custodian, RIAs may need to temporarily move these assets out of custody to unlock these rights. For example, some crypto assets can earn income through staking or yield farming, or have voting rights on protocol or network upgrade proposals. These differences from traditional assets pose new challenges to crypto asset custody.
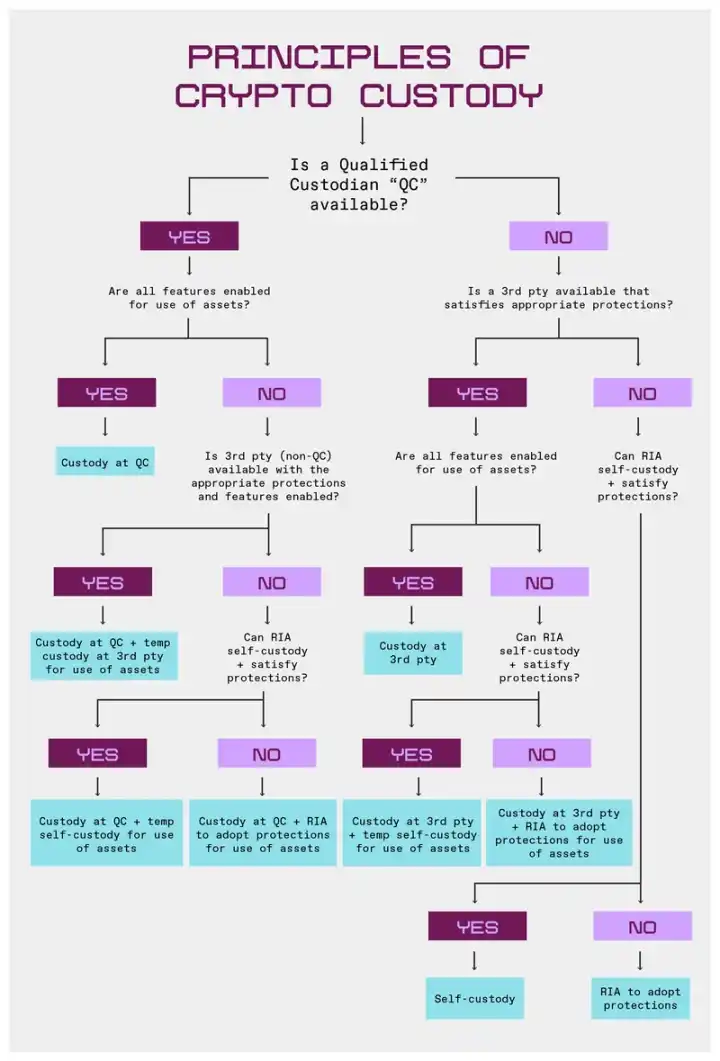
To facilitate determining when self-custody is appropriate, we have created this flowchart.
Principles
The principles we present here aim to demystify custody for RIAs while maintaining their responsibility to protect client assets. The current market for qualified custodians focusing on crypto assets (such as banks or broker-dealers) is extremely narrow. Therefore, our main focus is on whether the custodial entity has the capability to provide the substantive protective measures we believe are necessary for custody of crypto assets, rather than just the entity's legal status as a qualified custodian under the Investment Advisers Act.
We suggest that RIAs capable of meeting substantive protective measures may consider self-custody as an option when a third-party custodial solution that meets these requirements or supports economic and governance rights is unavailable.
Our goal is not to expand the scope of custody rules beyond securities. These principles apply to crypto assets that are considered securities and establish standards for RIAs' fiduciary duty for other asset types. RIAs should seek to hold non-security crypto assets under similar conditions and document custody practices for all assets, including reasons for significant differences in custody practices for different asset types.
Principle 1: Legal Status Should Not Determine Eligibility of Crypto Asset Custodians
Legal status and protective measures associated with specific legal statuses are crucial for a custodian's clients, but when it comes to crypto asset custody, this is not the only consideration. For example, federally chartered banks and broker-dealers are bound by custodial regulations that provide strict protections for clients, but state-chartered trust companies and other third-party custodians can also offer a similar level of protection.
A custodian's registration should not be the sole determining factor of its eligibility to custody crypto asset securities. In the crypto space, the scope of "qualified custodian" should be expanded to include:
- State-chartered trust companies (meaning they do not need to meet the "bank" definition standard under the Investment Advisers Act besides being subject to state or federal banking agency oversight and examination);
- Any entity registered under (proposed) federal crypto market structure legislation;
- Any other entity that can demonstrate adherence to strict client protection standards, regardless of its registration status.
Principle 2: Crypto Asset Custodians Should Establish Appropriate Protective Measures
Regardless of the technical tools used, custodians should implement specific protective measures around crypto asset custody. These measures include:
1. Segregation of Authority: Crypto asset custodians should not be able to withdraw crypto assets without the cooperation of RIAs.
2. Asset Segregation: Crypto asset custodians should not commingle assets held for RIAs with assets held for other entities. However, registered broker-dealers may use a single omnibus wallet, provided that they always maintain up-to-date records of ownership of these assets and promptly disclose the situation to the relevant RIAs.
3. Hardware Custody: The cryptographic asset custodian shall not use any custody hardware or other tools that pose a security risk or have a compromised risk.
4. Audit: The cryptographic asset custodian shall undergo at least annual financial and technical audits. Such audits shall include:
Financial audit by a PCAOB registered auditor:
Service Organization Control (SOC) 1 audit; SOC 2 audit; as well as confirmation, measurement, and reporting of cryptographic assets from a holder's perspective;
Technical audit:
ISO 27001 certification; penetration testing; as well as testing of disaster recovery procedures and business continuity planning.
5. Insurance: The cryptographic asset custodian shall have sufficient insurance coverage, or if insurance cannot be obtained, shall establish sufficient reserves.
6. Disclosure: The cryptographic asset custodian must annually provide RIAs with a major risk list related to its custody of cryptographic assets, as well as related written supervisory procedures and internal control measures to mitigate these risks. The cryptographic asset custodian shall review this quarterly to determine if disclosure updates are necessary.
7. Custody Jurisdiction: The cryptographic asset custodian shall not custody cryptographic assets in any jurisdiction where local laws stipulate that custodied assets will become part of the bankruptcy estate in the event of the custodian's bankruptcy.
Additionally, we recommend that the cryptographic asset custodian implement protective measures related to the following processes at each stage:
Preparation Stage: Review and assess the cryptographic assets to be custodied, including the key generation process and transaction signing process, whether it is supported by open-source wallets or software, and the source of every piece of hardware and software used in the key management process.
Key Generation: Encryption technology should be used at various levels of this process, and multiple cryptographic keys are required to generate a private key. The key generation process should be both "horizontal" (i.e., multiple cryptographic key holders at the same level) and "vertical" (i.e., multiple levels of encryption). Finally, statutory quorum requirements should also ensure the physical presence of authenticators.
Key Storage: Keys should never be stored in plain text but only in encrypted form. Keys must be physically isolated by geographical location or different access personnel. If hardware security modules are used to store key copies, they must meet Federal Information Processing Standards (FIPS) security ratings. Strict physical isolation and authorization measures should be implemented. The cryptographic asset custodian should maintain at least two levels of encrypted redundancy to ensure operation in the event of a natural disaster, power outage, or property destruction.
Key Usage: Wallets should require authentication; in other words, they should verify the user's identity and only allow authorized parties to access the wallet. Wallets should use mature open-source cryptographic libraries. Another best practice is to avoid using one key for multiple purposes. For example, keys for encryption and signing should be kept separate. Follow the principle of "least privilege," meaning that in the event of a security breach, access to any asset, information, or operation should be limited to only the parties absolutely necessary for the system to function.
Principle 3: The Cryptocurrency Asset Custody Rule should allow registered investment advisors to exercise economic or governance rights related to custody of cryptocurrency assets
Unless otherwise directed by the client, RIAs should be able to exercise economic or governance rights related to the custody of cryptocurrency assets. During the previous SEC administration, given the uncertainty surrounding token classification, many RIAs adopted a conservative strategy of custodian all cryptocurrency assets with a qualified custodian. As mentioned earlier, the available custodian market is limited, often resulting in only one qualified custodian willing to support a particular asset.
In these cases, RIAs may seek to exercise economic or governance rights, but the cryptocurrency asset custodian may choose not to offer these rights for various reasons. In turn, RIAs feel they do not have the power to choose another third-party custodian or self-custody to exercise these rights. These economic and governance rights include staking, yield farming, or voting.
Under this principle, we advocate that RIAs should select third-party cryptocurrency asset custodians that comply with relevant protective measures so that RIAs can exercise economic or governance rights related to the custody of cryptocurrency assets. If a third party cannot meet both of these requirements simultaneously, RIAs should not be seen as breaching custody by temporarily transferring assets for self-custody to exercise these rights.
All third-party custodians should make every effort to provide RIAs with the ability to exercise these rights while the assets are still under their custody and, when authorized by RIAs, take commercially reasonable action to exercise any rights related to on-chain assets.
Prior to transferring assets out for custody in order to exercise rights related to a specific cryptocurrency asset, RIAs or custodians must first determine in writing whether those rights can be exercised without transferring the assets out of custody.
Principle 4: The Cryptocurrency Asset Custody Rule should be flexible to achieve best execution
RIAs have a best execution obligation when trading assets. To this end, RIAs may transfer assets to a cryptocurrency trading platform to ensure the best execution of that asset, regardless of the asset's or custodian's status, provided that RIAs have taken the necessary steps to ensure the security of the trading venue, or RIAs have already transferred the cryptocurrency assets to an entity regulated under the cryptocurrency market structure legislation once finalized.
As long as RIAs determine that transferring cryptographic assets to an exchange for best execution is prudent, this transfer should not be viewed as relinquishing custody. This requires RIAs to reasonably determine that the exchange is suitable for best execution. If the trade cannot be properly executed on the exchange, the assets should be immediately returned to the cryptographic asset custodian.
Principle 5: In certain circumstances, RIAs should be allowed to self-custody.
While third-party custody should still be the primary choice for cryptographic assets, in the following circumstances, RIAs should be allowed to self-custody cryptographic assets:
· RIAs determine that they cannot find a third-party custodian that meets their required security measures;
· RIAs' self-custody arrangement is at least as effective as the protections available from third-party custodians;
· Self-custody is necessary for exercising any economic or governance rights related to cryptographic assets.
When RIAs decide to self-custody cryptographic assets for these reasons, RIAs must annually confirm that the circumstances warranting self-custody have not changed, disclose the self-custody arrangement to clients, and subject such cryptographic assets to the audit requirements of the Custody Rule.
Based on these principles, the cryptographic asset custody approach ensures that RIAs can fulfill their fiduciary responsibilities while accommodating the unique characteristics of cryptographic assets. By focusing on substantive protection rather than rigid categorization, these principles provide a practical path forward to safeguarding client assets and unlocking asset functionality. As the regulatory environment evolves, clear standards based on these protective measures will enable RIAs to responsibly manage cryptographic assets.
You may also like

46 minutes, $292 million stolen, DeFi faces development dilemma again

How to Earn Free USDT in 2026: No High Volume Required (WEEX Poker Party Guide)
Is Joker Crypto legit in 2026 or just another memecoin? Can You Really Earn Passive Income with Joker Crypto in 2026? Learn how Joker staking rewards work, how to earn NFT bonuses, expected APY ranges, gas-fee rebates, and how to avoid crypto scams before joining.

How to Get Free USDT Welcome Bonus in 2026: Earn Up to 700 USDT on WEEX
Legit Free Welcome Bonus 2026: Learn how to earn up to 700 USDT on WEEX with Auto Earn Boost Fest. Increase your balance, activate Auto Earn, and qualify automatically.

AI Agent Payments Just Got Real: Utexo × x402 Brings 50ms USDT Transactions to Internet Scale
Utexo integrates USDT into the x402 protocol, enabling 50ms instant payments embedded natively in HTTP requests. Explore how this breakthrough is rewriting the rules for AI agent payments, API monetization, and the machine-to-machine economy.

DWF Deep Report: AI in DeFi Outperforms Humans in Yield Optimization, but Complex Trades Still Lag Behind by 5 Times

What Separates Smart Money from the Crowd in Crypto? Insights from Freedom of Money
Most crypto traders lose money not because of bad luck, but because they misunderstand how the market really works. From Freedom of Money to the rise and fall of Sam Bankman-Fried, they highlight a key divide in crypto: those who build the market and those who chase it. This reading guide explores essential books that reveal how narrative, regulation, capital, and psychology shape long-term success in the crypto industry.

The Risk Management Core Team has just been ousted, and Aave is now facing a $200 million default.

The $293 million bug wasn't in the code; so, what's the deal with the "DVN Configuration Bug," which led to the largest hack of 2026?

a16z on Recruitment: How to Choose Between Crypto-Native and Traditional Talent?

The biggest DeFi heist of 2026, hackers easily took advantage of Aave

Will Robots Replace Humans? He Says No!

Binance Coin's Price Skyrockets 15x to All-Time High, Saved by Three Bull Market Lifelines

The organization has accessed the prediction market, but is stuck at the third stage

Head of crypto VC collective shrinks: a16z crypto fund management scale plummets by 40%, Multicoin cut in half

Arthur Hayes New Post: It's "No Trade" Time Now

Claude Opus 4.7 Review: Is It Worthy of the Title of Strongest Model?

DWF In-Depth Report: AI Outperforms Humans in Yield Farming Optimization in DeFi, But Complex Transactions Still Lag Behind 5x

The financial tricks of the crypto giant Kraken
46 minutes, $292 million stolen, DeFi faces development dilemma again
How to Earn Free USDT in 2026: No High Volume Required (WEEX Poker Party Guide)
Is Joker Crypto legit in 2026 or just another memecoin? Can You Really Earn Passive Income with Joker Crypto in 2026? Learn how Joker staking rewards work, how to earn NFT bonuses, expected APY ranges, gas-fee rebates, and how to avoid crypto scams before joining.
How to Get Free USDT Welcome Bonus in 2026: Earn Up to 700 USDT on WEEX
Legit Free Welcome Bonus 2026: Learn how to earn up to 700 USDT on WEEX with Auto Earn Boost Fest. Increase your balance, activate Auto Earn, and qualify automatically.
AI Agent Payments Just Got Real: Utexo × x402 Brings 50ms USDT Transactions to Internet Scale
Utexo integrates USDT into the x402 protocol, enabling 50ms instant payments embedded natively in HTTP requests. Explore how this breakthrough is rewriting the rules for AI agent payments, API monetization, and the machine-to-machine economy.
DWF Deep Report: AI in DeFi Outperforms Humans in Yield Optimization, but Complex Trades Still Lag Behind by 5 Times
What Separates Smart Money from the Crowd in Crypto? Insights from Freedom of Money
Most crypto traders lose money not because of bad luck, but because they misunderstand how the market really works. From Freedom of Money to the rise and fall of Sam Bankman-Fried, they highlight a key divide in crypto: those who build the market and those who chase it. This reading guide explores essential books that reveal how narrative, regulation, capital, and psychology shape long-term success in the crypto industry.


