Coinbase Experiences Insider Threat? $300 Million Scam Revealed, User Data Accurately Leaked
Original Title: "Over $300 Million Lost in One Year, Coinbase Users Repeatedly Targeted by Sophisticated Scams, Is There an Insider Leak Behind the Scenes?"
Original Author: Fairy, ChainCatcher
"Hello, this is the Coinbase Security Team. We have detected unusual activity on your account..."
The voice on the other end of the phone is professional and urgent, able to accurately state your name, registered email, and recent transaction history. Will you choose to hang up immediately, or follow the "customer service" guidance to gradually transfer your funds to a so-called "secure wallet"?
Recently, multiple Coinbase users have been consecutively scammed, with staggering losses. In March alone, the stolen funds have exceeded $46 million, and the annual losses for Coinbase users due to social engineering scams have reached over $300 million.
However, how exactly have these hackers been able to precisely target their victims? How have they obtained users' personal information? This security crisis may be even more severe than imagined.
Rampant Scams, Industrialized Phishing Attacks
On March 28, blockchain detective ZachXBT revealed that in the past two weeks, there have been multiple suspected cases of Coinbase users falling victim to scams, resulting in a total stolen amount in March exceeding $46 million.
In fact, such scams have long been evident. As early as the beginning of February, ZachXBT had previously disclosed that between December 2024 and January 2025, Coinbase users had lost as much as $65 million due to similar tactics, putting Coinbase at risk of facing over $300 million in social engineering scam losses annually.
According to ZachXBT's analysis, the scam tactics have formed a mature industrial chain:
1. Fraudsters Impersonate Coinbase Official
The scammers use a spoofed phone number to call the victim and leverage the user's personal information to gain trust. They claim that the user's account has experienced unauthorized login attempts, leading the victim to cooperate with security verification.
2. Sending Phishing Emails
The scammers send fake Coinbase emails containing a forged Case ID.
3. Guide User to Transfer Funds
The scammer asks the victim to transfer funds to a Coinbase Wallet and whitelist a scam address, claiming this is a form of account security verification.
4. Clone Coinbase Website
The scammer creates an almost 1:1 replica of the Coinbase phishing website and sends different operation prompts to the victim through forged emails and a Telegram scam panel.
In addition, according to Cointelegraph, several cryptocurrency users have recently received scam emails impersonating Coinbase and Gemini. These emails usually claim that due to regulatory requirements, users must transition to a self-hosted wallet and set April 1 as the deadline to create a sense of urgency.
The emails provide links to download the Coinbase Wallet or Gemini Wallet, along with pre-generated recovery phrases. Once users use these phrases to create a new wallet and transfer assets, the funds are instantly emptied by the scammer.
Internal Data Access Issues Surface
The core of social engineering scams lies in precise information gathering. In the Coinbase user scam cases, the attackers seem to have had access to victims' personal information, including phone numbers, email addresses, transaction records, etc. This raises a key question: how did this data fall into the hands of scammers?
Yesterday, The Block co-founder Mike Dudas claimed to have received an email from Coinbase on the X platform. The content of this email was unsettling, pointing directly to internal data access issues. The email stated:
"We are writing to inform you that we have detected signs indicating that a Coinbase employee may have accessed a small number of Coinbase customer accounts' records in a manner not consistent with internal policies, including your account."
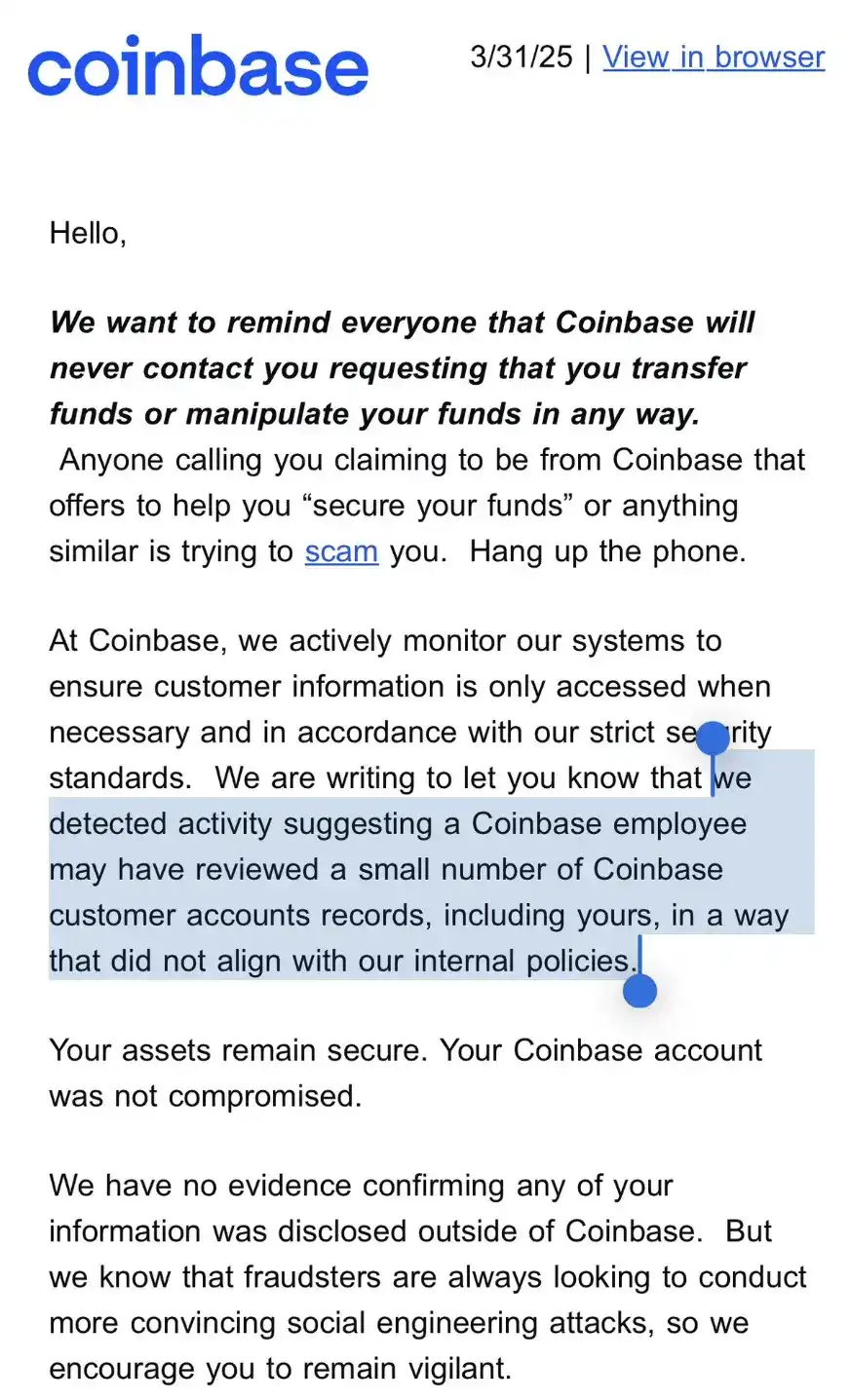
While the email stated, "Your assets remain secure, and your Coinbase account has not been compromised," and emphasized that there is currently no evidence of data leakage to external parties, this email issued a clear warning to users: internal data access issues have been confirmed and are not isolated incidents.
Dudas stated that this explains the phishing emails and calls pretending to be from Coinbase.
However, the scope of the data breach is questionable and may involve a larger set of users. Community user @ghaiankur stated: "I don't have any funds on Coinbase, and I have never used it. Yet I still received these emails because I have an account, so this may not just be targeting a few specific accounts but the entire database."
Data Breaches as an Industry Risk
Not only Coinbase, other exchanges also seem to face similar internal security vulnerabilities.
After Dudas shared the email, crypto trader Jordan Fish (@Cobie) revealed that the crypto exchange Kraken recently experienced a similar attack. He speculated: "This could be the attackers' strategy — to infiltrate the customer support team and internally steal user data."
Meanwhile, on March 27, the dark web news site Dark Web Informer disclosed that a hacker codenamed AKM69 claimed to have obtained a significant amount of private information of Gemini exchange users. The database contains 100,000 records, including the full names, emails, phone numbers, and locations of U.S. users, and even some data from Singapore and the U.K.

Either learn to protect users, or be abandoned by users.
When commenting on this incident, Solana co-founder toly suggested that exchanges should implement user-controlled transfer time locks to reduce the risk of assets being rapidly stolen. However, the essence of this event goes beyond that, exposing the internal risk control failures of exchanges and the highly industrialized nature of fraud.
Exchange security is no longer just a technical protection issue but also a matter of management and trust. In the face of increasingly sophisticated attack methods, establishing a more comprehensive risk control system will determine the future security standards of the industry.
You may also like

Stolen: $290 million, Three Parties Refusing to Acknowledge, Who Should Foot the Bill for the KelpDAO Incident Resolution?

ASTEROID Pumped 10,000x in Three Days, Is Meme Season Back on Ethereum?

ChainCatcher Hong Kong Themed Forum Highlights: Decoding the Growth Engine Under the Integration of Crypto Assets and Smart Economy

Why can this institution still grow by 150% when the scale of leading crypto VCs has shrunk significantly?

Anthropic's $1 trillion, compared to DeepSeek's $100 billion

Geopolitical Risk Persists, Is Bitcoin Becoming a Key Barometer?

Annualized 11.5%, Wall Street Buzzing: Is MicroStrategy's STRC Bitcoin's Savior or Destroyer?

An Obscure Open Source AI Tool Alerted on Kelp DAO's $292 million Bug 12 Days Ago

Mixin has launched USTD-margined perpetual contracts, bringing derivative trading into the chat scene.
The privacy-focused crypto wallet Mixin announced today the launch of its U-based perpetual contract (a derivative priced in USDT). Unlike traditional exchanges, Mixin has taken a new approach by "liberating" derivative trading from isolated matching engines and embedding it into the instant messaging environment.
Users can directly open positions within the app with leverage of up to 200x, while sharing positions, discussing strategies, and copy trading within private communities. Trading, social interaction, and asset management are integrated into the same interface.
Based on its non-custodial architecture, Mixin has eliminated friction from the traditional onboarding process, allowing users to participate in perpetual contract trading without identity verification.
The trading process has been streamlined into five steps:
· Choose the trading asset
· Select long or short
· Input position size and leverage
· Confirm order details
· Confirm and open the position
The interface provides real-time visualization of price, position, and profit and loss (PnL), allowing users to complete trades without switching between multiple modules.
Mixin has directly integrated social features into the derivative trading environment. Users can create private trading communities and interact around real-time positions:
· End-to-end encrypted private groups supporting up to 1024 members
· End-to-end encrypted voice communication
· One-click position sharing
· One-click trade copying
On the execution side, Mixin aggregates liquidity from multiple sources and accesses decentralized protocol and external market liquidity through a unified trading interface.
By combining social interaction with trade execution, Mixin enables users to collaborate, share, and execute trading strategies instantly within the same environment.
Mixin has also introduced a referral incentive system based on trading behavior:
· Users can join with an invite code
· Up to 60% of trading fees as referral rewards
· Incentive mechanism designed for long-term, sustainable earnings
This model aims to drive user-driven network expansion and organic growth.
Mixin's derivative transactions are built on top of its existing self-custody wallet infrastructure, with core features including:
· Separation of transaction account and asset storage
· User full control over assets
· Platform does not custody user funds
· Built-in privacy mechanisms to reduce data exposure
The system aims to strike a balance between transaction efficiency, asset security, and privacy protection.
Against the background of perpetual contracts becoming a mainstream trading tool, Mixin is exploring a different development direction by lowering barriers, enhancing social and privacy attributes.
The platform does not only view transactions as execution actions but positions them as a networked activity: transactions have social attributes, strategies can be shared, and relationships between individuals also become part of the financial system.
Mixin's design is based on a user-initiated, user-controlled model. The platform neither custodies assets nor executes transactions on behalf of users.
This model aligns with a statement issued by the U.S. Securities and Exchange Commission (SEC) on April 13, 2026, titled "Staff Statement on Whether Partial User Interface Used in Preparing Cryptocurrency Securities Transactions May Require Broker-Dealer Registration."
The statement indicates that, under the premise where transactions are entirely initiated and controlled by users, non-custodial service providers that offer neutral interfaces may not need to register as broker-dealers or exchanges.
Mixin is a decentralized, self-custodial privacy wallet designed to provide secure and efficient digital asset management services.
Its core capabilities include:
· Aggregation: integrating multi-chain assets and routing between different transaction paths to simplify user operations
· High liquidity access: connecting to various liquidity sources, including decentralized protocols and external markets
· Decentralization: achieving full user control over assets without relying on custodial intermediaries
· Privacy protection: safeguarding assets and data through MPC, CryptoNote, and end-to-end encrypted communication
Mixin has been in operation for over 8 years, supporting over 40 blockchains and more than 10,000 assets, with a global user base exceeding 10 million and an on-chain self-custodied asset scale of over $1 billion.

$600 million stolen in 20 days, ushering in the era of AI hackers in the crypto world

Vitalik's 2026 Hong Kong Web3 Summit Speech: Ethereum's Ultimate Vision as the "World Computer" and Future Roadmap

On the same day Aave introduced rsETH, why did Spark decide to exit?

Full Post-Mortem of the KelpDAO Incident: Why Did Aave, Which Was Not Compromised, End Up in Crisis Situation?

After a $290 million DeFi liquidation, is the security promise still there?

ZachXBT's post ignites RAVE nearing zero, what is the truth behind the insider control?

Vitalik 2026 Hong Kong Web3 Carnival Speech Transcript: We do not compete on speed; security and decentralization are the core

In-depth Analysis of RAVE Events: Short Squeeze, Crash, and Quantitative Financial Models of Liquidity Manipulation



